Bitdefender Threat Debrief | August 2023

MDR Insights: Understanding the Threat Landscape
In our previous discussion about Threat Modeling and its application in Bitdefender MDR’s intelligence monitoring, we emphasized the importance of considering the threat landscape. This term refers to the overall picture of potential cybersecurity threats and risks faced by individuals, organizations, or systems, including various cyberattacks, vulnerabilities, and potential adversaries. A clear grasp of the threat landscape is instrumental in identifying, assessing, and mitigating security risks.
But how does an organization perform this assessment?
In the process of threat modeling, the foundation is laid through analyst research and information collection, which then guides activities such as monitoring, baselining, and threat hunting. Armed with this data, a shift from a defensive to an offensive mindset is required—think like an attacker. Here are seven key considerations for this exercise:
- Past Targeting: Analyze previous attacks, successful or not, to dissect the attack vectors, targets, and strategies.
- Motivations for Targeting: Delve into potential reasons for your company being a target, including financial gain, disruption, theft, or espionage.
- Affiliations and Third Parties: Assess affiliations with third parties that could make your company vulnerable if they’re compromised.
- Adversarial Tactics: Discuss how an adversary might approach their goals, exploiting weaknesses like inadequate asset management or outdated technology.
- Technical Preparedness: Scrutinize your technical setup for vulnerabilities, patching, user training, and incident response plans.
- Adapting to Changes: Consider how local or global events could impact your operations and remote work, aligning cybersecurity measures accordingly.
- Industry Insights: Investigate cyberattack trends affecting your industry and geographic location.
Taking this exploratory approach provides clarity to your attack surface. Imagine the fictional ACME BANKS R Us (ABRU) adopting this methodology. They’d acknowledge the persistent threat of financially motivated groups deploying banking malware and ransomware. Phishing and social engineering also enter their radar as potential vulnerabilities. ABRU’s technology stack becomes a potential weak point, necessitating consistent maintenance to thwart exploitation. Threat actors exploit vulnerabilities, even having preferred admin tools like PsExec to execute programs remotely.
The concept of a threat landscape introduces an added layer of understanding, considering possibilities that may not have initially been apparent in threat modeling. Recognizing risks and the assets demanding protection informs decisions on security tools, training, and processes, fortifying defenses against potential attacks and positioning for success during security incidents.
Ransomware Report
Spear phishing attacks are often used as an initial attack vector and ransomware infection is often the final stage of the kill chain. For this report, we analyzed malware detections collected in July 2023 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
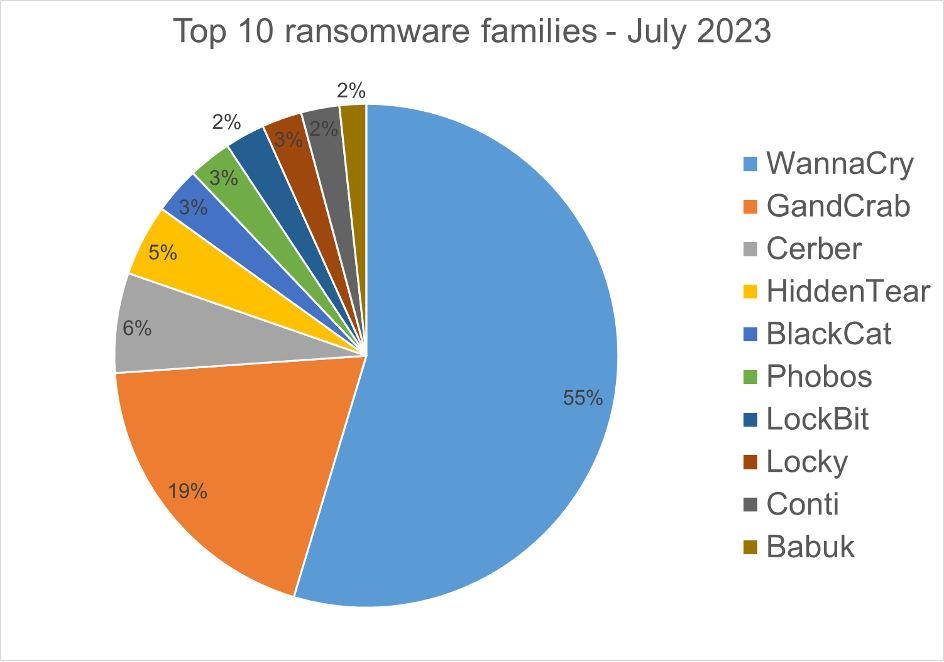
Top 10 Ransomware Families
We analyzed malware detections from July 1 to July 31, 2023. In total, we identified 227 ransomware families. The number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.
Top 10 Countries
In total, we detected ransomware from 136 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of a population is correlated to the number of detections.

Android trojans
Below are the top 10 trojans targeting Android we have seen in our telemetry during July 2023.

Triada.LD – Malware that gathers sensitive device information (such as Device IDs, Subscriber IDs, MAC addresses) and then sends it to a control-and-command (C&C) server. The C&C server responds by sending back a link to a payload that malware will download and execute.
Downloader.DN – Repacked applications taken from Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
Triada.LC – Malware that gathers sensitive information about a device (Device IDs, Subscriber IDs, MAC addresses) and sends them to a malicious C&C server. The C&C server responds by sending back a link to a payload, which the malware then downloads and executes.
InfoStealer.SO – Applications that exfiltrate users’ text messages on a regular basis.
SMSSend.AYE – Malware that tries to register as the default SMS application on the first run by requesting the consent of the user. If successful, it collects the user’s incoming and outgoing messages and forwards them to a C&C server.
Banker.XO – Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express, etc.). Once installed, it locates banking applications installed on the device and tries to download a trojanized version from the C&C server.
InfoStealer.AAL – Remote Administration Tool for mobile devices that allows an attacker to take control of a victim’s device without needing root access. Once the malware is installed on the phone, the attacker can carry out various attacks that compromise the confidentiality and privacy of the victim’s data. The tool has the ability to capture the screen content, stream live video from the phone’s cameras, upload and download files from the device, and track the user’s location.
Banker.XX – Applications that impersonate Korean banking applications to record audio and video, collect sensitive information (SMS messages, contacts, GPS location…) and upload it to a C&C server.
SpyAgent.DW – Applications that exfiltrate sensitive data like SMS messages, call logs, contacts, or GPS location.
Marcher.AV – Applications that disguise themselves as Play Store applications. The malware tries to ask for accessibility permissions to capture keystrokes and also uses the VNC screen recording function to log the user’s activity on the phone.
Homograph Phishing Report
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about the “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.
