Bitdefender Threat Debrief | October 2023

Even as October’s Cybersecurity Awareness Month floods the internet with articles and campaigns about the importance of online safety, we’ve observed a surprising increase in user-driven security incidents. This is especially alarming because one would expect such incidents to decline, rather than spike, during a month dedicated to cybersecurity education.
“User-driven security incidents” refer to cybersecurity incidents caused by individuals, often due to a lack of awareness or inadvertent actions. Over 70% of recent incidents investigated by the Bitdefender MDR team involved human error, stemming from three primary causes: phishing, malicious downloads, and malicious URLs. These incidents highlight the critical need for user education, awareness, and security measures to mitigate the risks associated with human actions, ultimately preventing potential security breaches.
Many incidents originate from unmonitored network segments or systems lacking standard security policies, often due to human choices. In many cases, employees who are the most resistant to following the security guidelines are often the ones who need them the most. The reluctance to establish consistent policies often results from a lack of understanding about the associated risks or a conscious decision to accept those risks. Unmonitored segments may be also a matter of financial considerations, and the deployment of agents could be limited to what’s perceived as the most critical or high-risk devices.
To address these challenges and reduce the risk of user-driven security incidents, here are five key recommendations:
- Simplify and Clarify: Ensure cybersecurity recommendations are simple, clear, and actionable. Avoid technical jargon and provide easy-to-follow guidance.
- Relevance and Customization: Tailor your cybersecurity messaging to your specific audience, considering their technical expertise and security awareness.
- Engagement and Education: Use engaging content such as videos and real-life scenarios to make security practices relatable and memorable.
- Consistency and Regular Reminders: Reinforce cybersecurity practices year-round, rather than relying solely on a single awareness month.
- Continuous Learning and Feedback: Implement ongoing training, simulated exercises, and provide feedback to users to keep them updated and motivated to follow security best practices.
Ransomware Report
Spear phishing attacks are often used as an initial attack vector and ransomware infection is often the final stage of the kill chain. For this report, we analyzed malware detections collected in September 2023 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
Top 10 Ransomware Families
We analyzed malware detections from September 1 to September 30. In total, we identified 268 ransomware families. The number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.

Top 10 Countries
In total, we detected ransomware from 151 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of a population is correlated to the number of detections.

Android trojans
Below are the top 10 trojans targeting Android we have seen in our telemetry during September 2023.

Triada.LD – Malware that gathers sensitive device info (Device IDs, Subscriber IDs, MAC addresses) and then sends it to a C&C server. The C&C server responds by sending back a link to a payload, that malware will download and execute.
SMSSend.AYE – Malware that tries to register as the default SMS application on the first run by requesting the consent of the user. If successful, it collects the user’s incoming and outgoing messages and forwards them to a Command & Control (C&C) server.
SpyAgent.IN – Applications that exfiltrate sensitive data like SMS messages, call logs, contacts, or GPS location.
Downloader.DN – Repacked applications taken from the Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
Banker.AFX – Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express …). Once installed, it locates banking applications installed on the device and tries to download a trojanized version from the C&C server.
Triada.LC – Malware that gathers sensitive information about a device (Device IDs, Subscriber IDs, MAC addresses) and sends them to a malicious C&C server. The C&C server responds by sending back a link to a payload that the malware downloads and executes.
Marcher.AV – Applications that disguise themselves as Play Store applications. The malware tries to ask for accessibility permissions to capture keystrokes and also uses the VNC screen recording function to log the user’s activity on the phone.
InfoStealer.SO – Applications that exfiltrate users’ text messages on a regular basis.
Banker.XO – Polymorphic applications that impersonate legit apps (Google, Facebook, Sagawa Express …). Once installed, it locates banking applications installed on the device and tries to download a trojanized version from the C&C server.
Banker.AGY – A new Android malware family, known as “Godfather,” is designed to gather sensitive information such as SMS messages, app data, and phone numbers. It can also manipulate the device’s screen using VNC, divert calls, and introduce fake banking URLs.
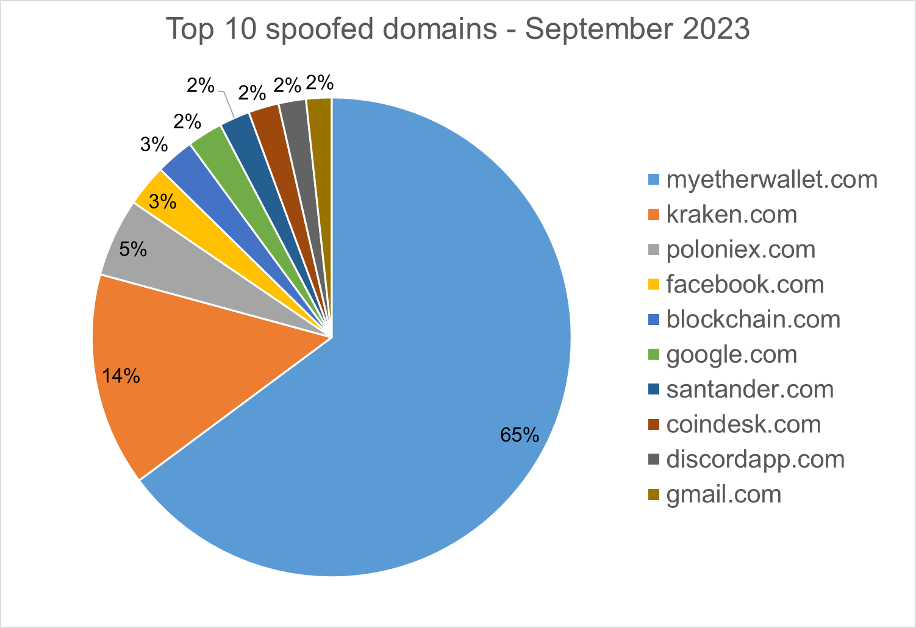
Homograph Phishing Report
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about the “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.